Services
Products
Cybersecurity
Contact
PL

An automated tool that searches the darkest corners of the Internet for data
belonging to your organization. Find out what was stolen from you.
Access to the world's largest commercial database of of darknet content - updated on a regular basis
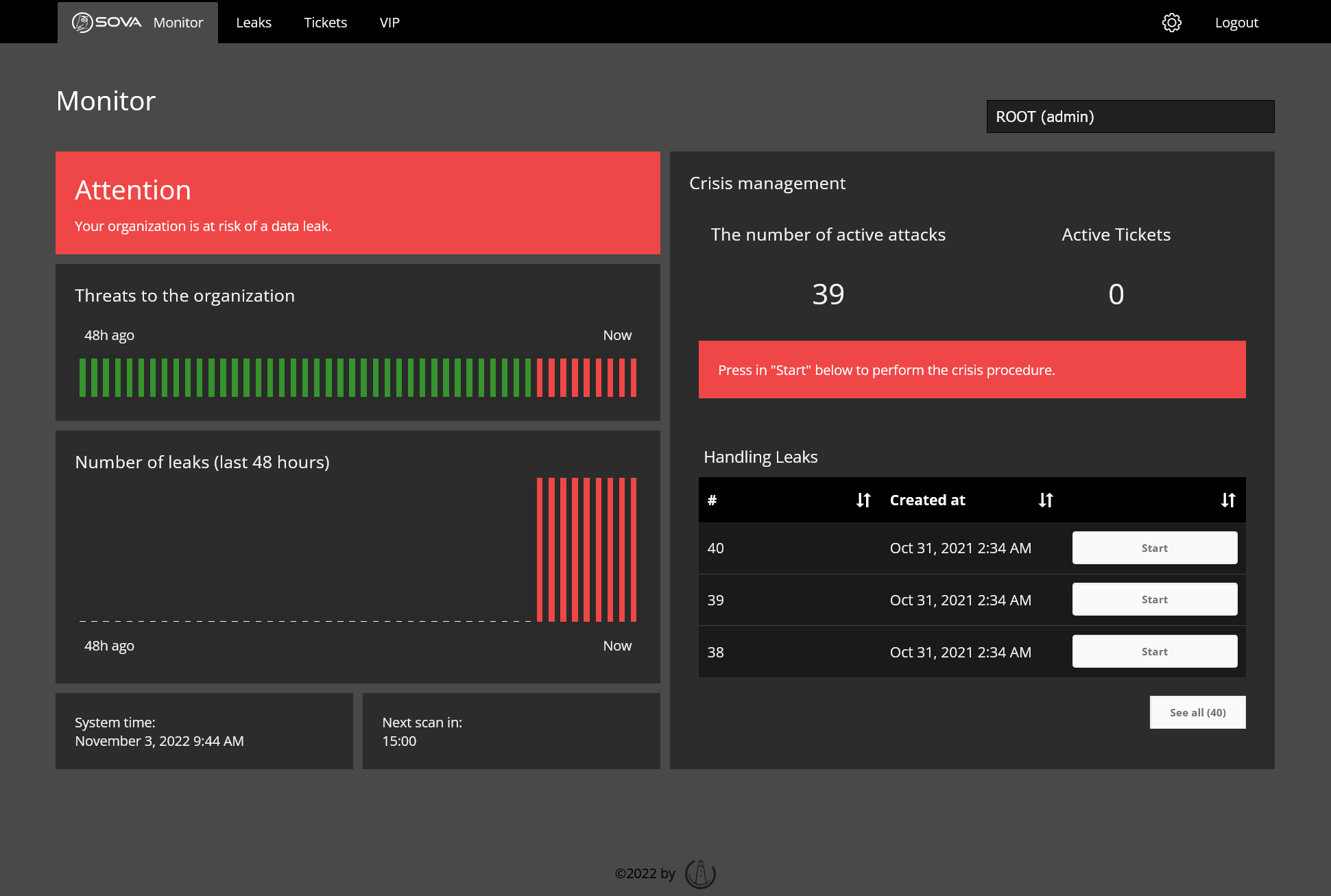
Alert system for detected incidents via SMS, e-mail and API
Ability to suspect and analyze leaks found and take immediate action
TOR network records
New darknet pages indexed per
hour
Unique email addresses
SOVA is a web-based application that allows secure analysis and search of content in the darknet.
SOVA is a a web-based application that allows secure analysis and search of darknet content.
SOVA has access to the world's largest commercially available database of content from the darknet, which is constantly updated with structured, real-time data.
It allows us to to effectively monitor the darknet for leaks containing domains, words keys, or specific phrases.
You determine for yourself what
you are looking for. You choose the monitored phrases and time intervals.
The application is fully
automatic. From the very first minutes it searches the bases and does so for as long as you
you want.
We will inform you about
any incident found. Inside the application you can analyze it and
manage it.
Do you want to search for
specific data? No problem, you can also direct queries to the database
manually.
Access to
The world's largest database of stolen information
Many existing solutions that collect content from the darknet have limited access and index only the home pages of of most sites. With a combination of account-level access and advanced machine learning technology, 99% of all collected data in the database goes "deeper" than the homepage of websites.
In fact, it is estimated that 60% of all data
comes from sources that require some form of authentication or access at the
account level. When looking for leaks, this is a very important factor, because
sensitive data published or sold on the Internet is often only available to
to logged-in/verified accounts.
Every day we collect millions of documents from the darknet and networks
adjacent networks. We obtain our data from: TOR, I2P, Zero Net, Telegram, IRC, pastebin,
high-risk surface networks, darknet marketplaces, hacking forums,
encrypted chat platforms, as well as other authenticated services that we
we cannot disclose in order to protect the uninterrupted source of collected data.


SOVA has the option
alerting about finding new leaks via
SMS, e-mail or API channels communicating directly with the existing system
IMS.
Inside the platform allows you to manage such security incidents through
assigning specific leaks as tasks for specific administrators.
Platform
allows you to configure the monitoring of new content at any time intervals and
manual database search on demand